
International Journal of Engineering and Advanced Technology (IJEAT)
ISSN: 2249-8958 (Online), Volume-8 Issue-5C, May 2019
1332
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
Abstract:- Requirements Engineering phase is well recognized
as a root of Software Development Life Cycle (SDLC) by
research community. Requirements are elucidated through
requirements elicitation methods conceded by requirement
analyst. Requirements elicitation phase is planned and
strategized to get complete acquaintance about user’s
requirements and expectations. Current software industries
having massive necessity to help requirements analyst in
requirements elicitation process to carry out precise manner.
Correct and refined requirements lead to successful software
projects. Vague and incorrect requirements possibly will result in
the defective software project. For successful software
development, it is vital to recognize precise and accurate
requirements for the software project. The progression of
information technology has presented various requirements
elicitation techniques and therefore analysts are provided with
various likely options. Generally, the analyst selects elicitation
technique according to company practice or their individual
knowledge and skills. It is undefined on the selection of best
elicitation techniques for certain situations under particular
constraints and circumstances. Several guidelines do exist in
literature for technique selection but most technique are
theoretical rather than practical.
In this research paper, deep knowledge of principal elicitation
techniques is explained. After that a five facets model is proposed
to select elicitation technique in which major aspects are project
characteristics, software development process categories,
organizational characteristics, stakeholder characteristics and
analyst characteristics. We also demonstrate the suitability of the
proposed framework via case studies and verified how the model
uses relative knowledge of problem domain to select appropriate
requirements elicitation technique for the software under
construction.
Index Terms: Software Development Life Cycle, Software
Engineering, Requirements Engineering, Requirements
Elicitation, Research Framework, Techniques Selection.
I. INTRODUCTION
In the existing expanding information technology trends,
industries endurance depends on the excellence of the
software products delivered to customer. Software
Engineering Body of Knowledge (SWEBOK) [1] define
Manuscript published on 30 May 2019.
* Correspondence Author (s)
Mona Batra,
1
Research Scholar, Department of Computer Science and
Engineering, Birla Institute of Technology, Mesra, Ranchi, Jaipur Campus,
Rajasthan, India.(Email id: monabatra89@gmail)
Archana Bhatnagar, Asst. Professor, Department of Computer Science
and Engineering, Birla Institute of Technology, Mesra, Ranchi, Jaipur
Campus, Rajasthan, India.(Email id: abhatnagar@bitmesra.ac.in)
© The Authors. Published by Blue Eyes Intelligence Engineering and
Sciences Publication (BEIESP). This is an open access article under the
CC-BY-NC-ND license http://creativecommons.org/licenses/by-nc-nd/4.0/
software development process as a blend of Requirements
gathering, requirements analysis, designing, software
architecture, implementation and maintenance. Large variety
of tasks accomplished to grasp the requirements are
acknowledged as Requirements Engineering [5]. It
encompasses discovery of goals, requirements, potential
viewpoints of stakeholders and communicate them to the
developers [6]. Requirements describe the functional and
non-functional facet of software system, all facilities it
offers and the boundary conditions on its operative
-
environment [3]. This phase of software development life
cycle supports requirements analyst to grasp the actual need
of software system and build an economic system [4].
Various researchers and practitioners describe different
facets of Requirements Engineering (RE) process.
According to SWEBOK [1] requirements engineering
activities involve Requirements Elicitation, Analysis of
requirements, Requirements Specification, Requirements
Verification and Management. Pohl's define following steps
in requirements modelling: Requirements Elicitation,
Negotiation, Specification of requirements, Documentation
and Requirements Verification/Validation [7].
Sommerville's requirements model comprised of
Requirements Acquisition, Specification, Validation and
Documentation of requirements [3]. Wiegers’s RE model
[8] splits whole RE activities into two fragments. First is
Requirements Development and second is Requirements
Management. Requirements Development activity consists
of requirements elicitation, Analysis, Specification and
Verification. Proper understanding of each requirements
engineering process model and techniques are essential for
effective software development [9]. Efforts and cost can be
reduced by implementing the security aspect right from the
beginning i.e. from the requirement phase itself [10].
Our work emphases on software requirements elicitation.
Requirements elicitation phase is the initial and the utmost
vital phase in requirements engineering process [2]. It is
concerned with gathering of requirements for the software
under creation. Bohem [15] defines requirements elicitation
is the prime stage in requirements engineering process if not
done properly leads to deprived quality of products, missing
deadlines and high product costs. Loucopoulos et al.
describe requirements elicitation as the practice to findng all
appropriate facts to develop a structure of a problem related
to particular domain [13]. Borland define requirements
elicitation as the facility to work collectively with all
stakeholders to determine product needs, vision and goals of
proposed project [14].
Requirements Elicitation Technique Selection: A
Five Factors Approach
Mona Batra
, Archana Bhatnagar
International Conference on Recents Advancements in Engineering and Technology (ICRAET-18) |15th and 16th
March 2019|Siddhartha Institute of Technology & Sciences, Telangana, India.
1333
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
According to Mulla et al. [2] requirements elicitation
process consists of following phases: (1) Identification of
requirements sources (2) Accumulate the wish list for
individual corresponding part (3) Documentation and
refinement of the wish list (4) Integrate the wish lists of all
other stakeholders and (5)
Identify the non-functional requirements. Bell et al. [12]
observed in their study that requirements for system
development would not rise spontaneously but they
essentially engineered and need constant modification as
well as evaluations.
Comprehensive and organized requirements can make
software projects more consistent. This is significantly
influenced by the techniques used during requirements
elicitation process [3]. Any application development is
essentially required incorporation of good requirements
elicitation practices. There are number of techniques exists
in literature like interview, brainstorming, protocol analysis,
survey, observation analysis laddering etc.
[17][18][19][20][21][22][23][24][25]. Requirements
elicitation techniques selection for a certain software project
domain is a challenging task. A variety of components
influence the selection process. There is not a single
flawless elicitation technique that can satisfy each and every
condition, as there is no agreement among software experts
on the selection of finest elicitation technique to elicit
information. Deep literature review conducted by authors
[11] suggested to incorporate application specific elicitation
technique for successful software development and
management.
To overcome this problem, we are proposing an approach
that focuses on the important factors that affect requirements
elicitation process. We have exposed both the present theory
and the results of experimental research to design the
approach. We have also used our own experience and
expertise for designing this framework. The paper aims to
provide a guide for selecting the correct requirements
elicitation techniques based on the above factors. The
attributes of all the factors are based on from literature
surveys, case studies and in-depth discussion with software
experts.
The paper is formed in four sections. Next section
presented the brief information about the requirement
elicitation techniques along with strength and weaknesses.
Section III, proposed approach for selecting requirements
elicitation technique. Working of the proposed framework is
explained with the support of case studies in section IV. At
the end conclusion is presented in section V.
II. REQUIREMENTS ELICITATION
TECHNIQUES
Academicians, experts and practitioners are working in
the area of requirements engineering. They mainly focused
in the direction of improving the complex requirements
elicitation process with the progress of various techniques,
practices and tools. Quite a lot of these techniques have been
occupied and adopted from other fields like social sciences
but only limited number of techniques have been selected
for requirements elicitation [16]. This segment describes the
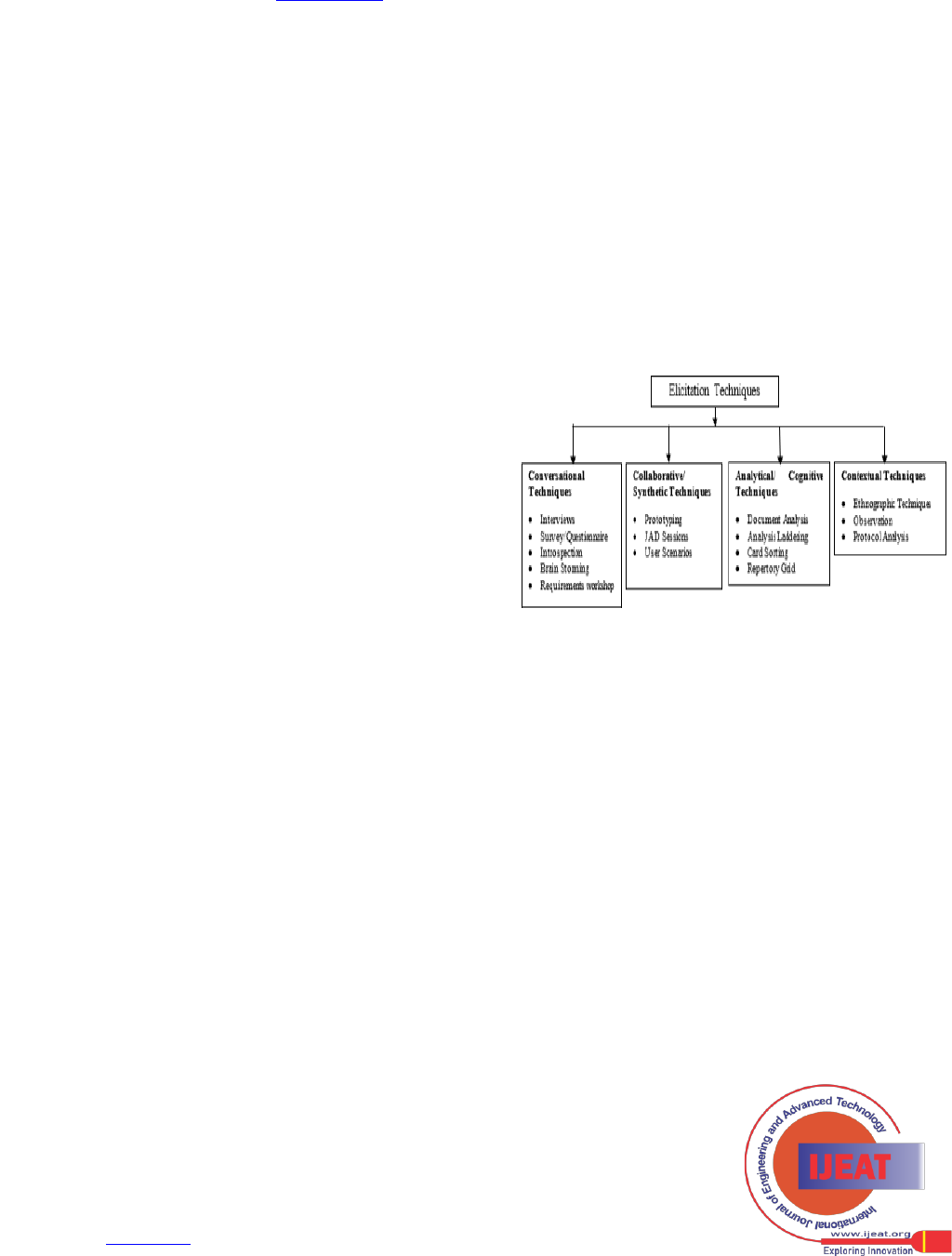
classification of requirements elicitation methods.
Requirements development is done thorough numerous
interactions between stakeholders and requirements analysts
[17]. According to the means of communication
requirements elicitation techniques are categorized into four
types: Conversational, Collaborative, Analytic, and
Contextual techniques
[17][18][19][20][21][22][23][24][25]. Each category
signifies a particular interaction model between stakeholders
and requirements analyst and also depicts the nature of a
method.
This section exemplifies basic details of requirements
elicitation techniques along with their strengths and
weaknesses. Requirements elicitation techniques can be
categorized into four types [26]:
Figure 1: Requirements Elicitation Techniques
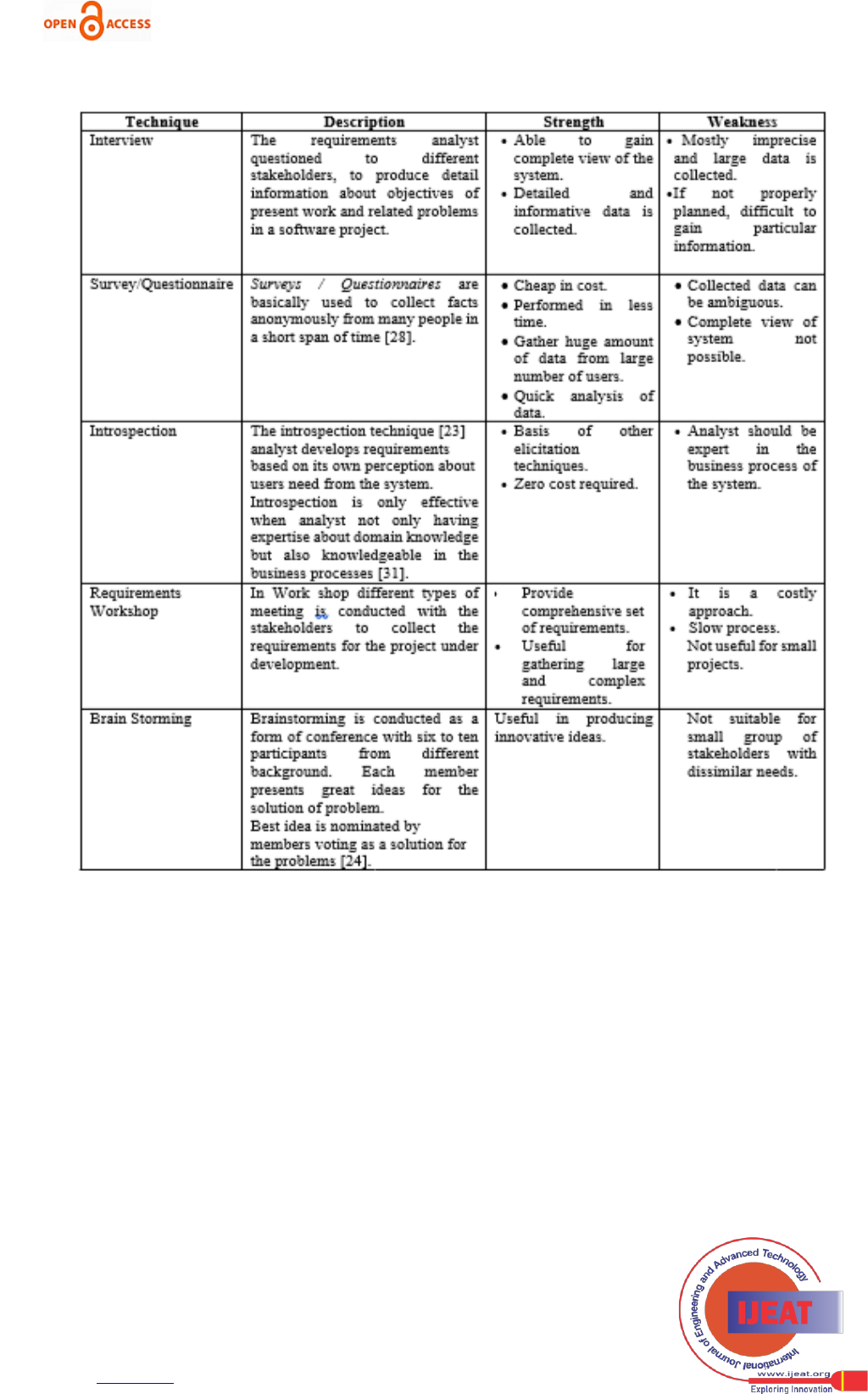
A. Conversational (Traditional) Techniques:
The conversational method also known as traditional
methods or verbal methods [1] typically describe the oral
communication among two or more people. Conversation is
an ordinary means to express requirements and ideas, via
asking questions and replying to the particular questions. Its
main focus is to understand problem in details and gather
requirements for generic products. Details of traditional
techniques are described in the table below:
International Journal of Engineering and Advanced Technology (IJEAT)
ISSN: 2249-8958 (Online), Volume-8 Issue-5C, May 2019
1334
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
Table 1: Traditional Requirements Elicitation Techniques
B. Collaborative Techniques
It is also called as Synthetic methods. The synthetic
methods integrate various communication channels, and
suggests models to demonstrate the characteristics and
relationship of system.
International Conference on Recents Advancements in Engineering and Technology (ICRAET-18) |15th and 16th
March 2019|Siddhartha Institute of Technology & Sciences, Telangana, India.
1335
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
Table 2: Collaborative Requirements Elicitation Techniques
C. Cognitive Techniques
Cognitive techniques make use of present system
documentation to capture requirements. It discovers expert’s
acquaintance of current system and obtain requirements
from sequence of assumptions carried out for gather large
information about problem domain.
Table 3: Cognitive Requirements Elicitation Techniques
International Journal of Engineering and Advanced Technology (IJEAT)
ISSN: 2249-8958 (Online), Volume-8 Issue-5C, May 2019
1336
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
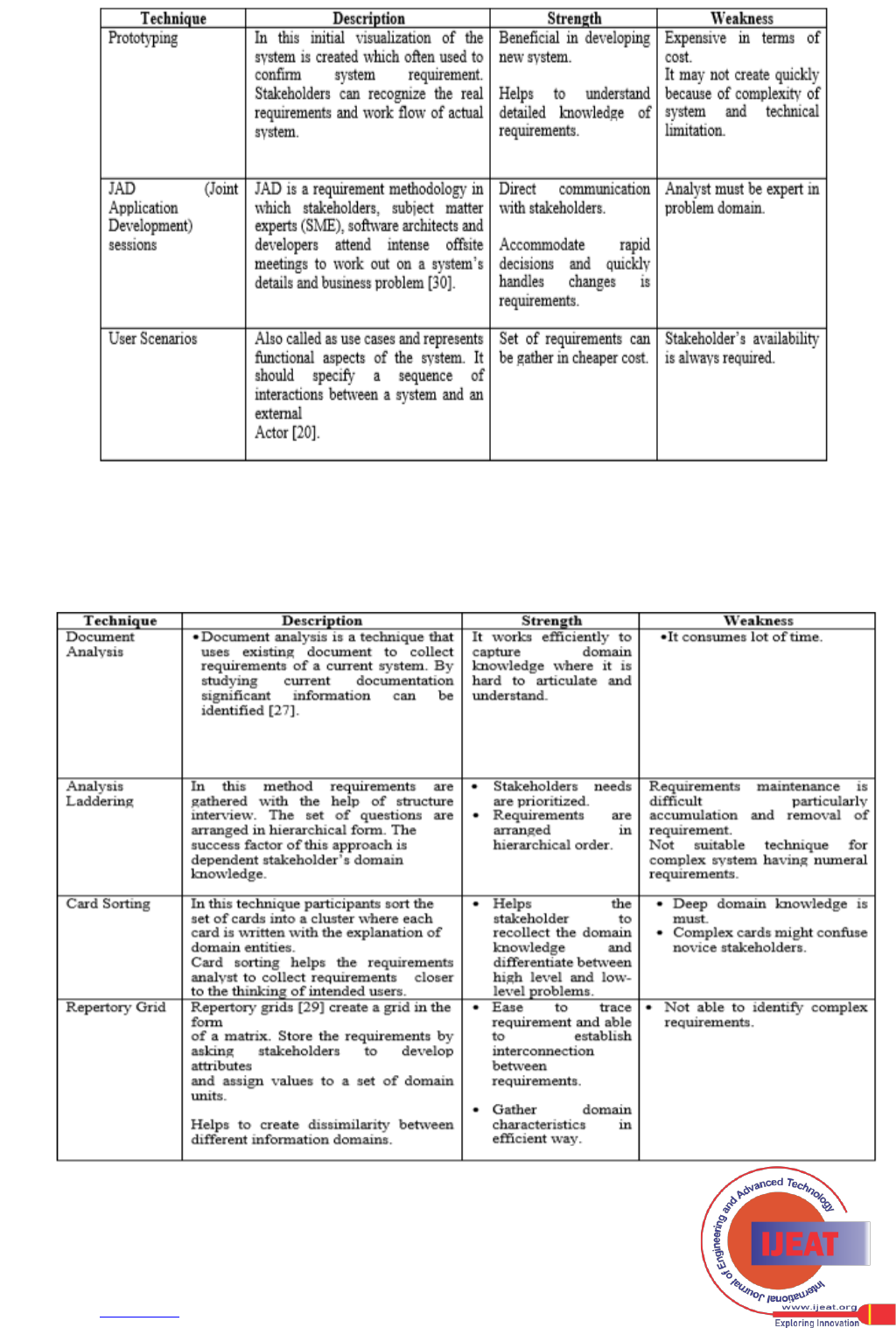
D. Observational Techniques
Observation methods gather information by surveil
human actions at the atmosphere wherever software system
is expected to be placed in case of new system or already
located, in the case of present system.
Table 4: Collaborative Requirements Elicitation Techniques
III. PROPOSED APPROACH FOR SELECTING
REQUIREMENTS ELICITATION TECHNIQUE
For the development of the framework, we have studied
the facts of requirements elicitation techniques with respect
to software project, software development process,
organization culture, stakeholders’ characteristics and
analyst attributes with the help of research work of
academicians, experience reports of software experts,
project reports and experts’ advices. The working of the
framework can be explained as below:
Figure 2: Proposed approach for selecting requirements elicitation technique

International Conference on Recents Advancements in Engineering and Technology (ICRAET-18) |15th and 16th
March 2019|Siddhartha Institute of Technology & Sciences, Telangana, India.
1337
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
1) We have identified several significant traits for
each of the five factors that influence the selection process.
The five factors are project, stakeholder, analyst,
organization and software development process.
2) We have constructed an attribute table for all five
factors. Each table having the attribute name and its value.
Values are assigned according to literature work, real-life
software project report and expert advice.
3) We construct a mapping table for each attribute of the
above mentioned five factors and their association with the
elicitation techniques. Mapping table act as a decision
system to select of elicitation technique for a given problem
domain.
4) Problem domain comprises of some known
characteristics that comes from feasibility study before
requirements elicitation process begins. Figure 1 depicted
the proposed framework.
5) List of Attributes chosen for each factor table is listed
below:
A. Project Characteristics
Project characteristics plays an important role for
selecting requirements elicitation techniques. Ten project
attributes have been considered for the analysis of each RE
technique. The first attribute is Project Size and the values
associated with this are Small, Medium, Large. The second
attribute is Project Complexity and its associated values can
be Low, Medium, High. Third attribute is Time Constraints
and its associated value can be Low, Medium or High.
Fourth attribute to consider is Cost Constraints and it can be
Low, Medium, High. Fifth attribute is Project Category and
project can be Organic, Semidetached, Embedded. Sixth
attribute is Project Status and project can be existing or new.
Seventh attribute is Project Scope that can be either Public
or Private. Eighth attribute is Requirements Volatility that
describe change is number of requirements and it can be
Small, Medium or Large. Ninth attribute is Project Safety
that can be Low, Medium or High. Last and tenth attribute is
User involvement it can be Low, Medium or High. Each
value can be ranged according to Probability. In statistics,
probability lies between 0 to 1. Graph 1 depicted the
association between Requirements elicitation techniques and
Project Characteristics.
Graph 1. Elicitation Techniques Vs Project Characteristics
B. Organization Characteristics
Organizational characteristics reflect significant role
while selecting requirements elicitation techniques.
Organizational features that affects overall working of
software development. The Organization attributes that has
been considered for the analysis of each elicitatiom
technique are organization size (Small, Medium; Large.
Organization and customer relationship (New or existing),
Impact of organizational culture (Yes, No). Graph 1
depicted the association between Requirements elicitation
techniques and Organizational Characteristics.

International Journal of Engineering and Advanced Technology (IJEAT)
ISSN: 2249-8958 (Online), Volume-8 Issue-5C, May 2019
1338
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
Graph 2. Elicitation Techniques Vs Organizational Characteristics
C. Software Development Process Model Characteristics
There are lots of software development process model
exist in literature. The most popular software process
models are: Waterfall oftware Development Model, Spiral
Model, Prototype Model, Rapid Application Development
process model, Extreme Programming (XP), Scrum.
The software processes also impacted on the selection of
elicitation techniques. Below, Graph 3 depicts the relation
between process model and elicitation techniques.
Applicability is ranged between 0 to 1. If a specific process
model scores 1 for any elicitation technique that means that
technique gives the accurate requirements with respect to
specific process model. If it scores 0 that that requirements
elicitation technique gives ambiguous results. Moderate
results between 0 to 1.
Graph 3. Elicitation Techniques Vs Software Process Characteristics
D. Stakeholder Characteristics
Stakeholder possessed most important role in developing
effective software. Attributes chosen for the analysis of
stakeholder characteristics are: Geographical distribution
(same location, different location), number of stakeholder
(single, group), Stakeholder Availability (Yes, No),
Stakeholder Experienced (Fresher, Experienced),
Stakeholder Knowledge (Low, Medium, High), Stakeholder
Expressiveness (Low, Medium, High). The Graph 4 depicts
the relationship between stakeholder characteristics and
requirements elicitation techniques.
0
0.2
0.4
0.6
0.8
1
1.2
Organizational Characteristics
Organization size(Small=0; Medium=0.5; Large=1; S/M=0.33; M/L=0.75; S/L=0.4; S/M/L=1)
Organization and customer relationship (New=0, Existing=1, New/Existing=0.5)
Impact of organizational culture(Yes=1,No=0)

International Conference on Recents Advancements in Engineering and Technology (ICRAET-18) |15th and 16th
March 2019|Siddhartha Institute of Technology & Sciences, Telangana, India.
1339
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
Graph 3. Elicitation Techniques Vs Stakeholder Characteristics
E. Analyst Characteristics
Analyst is a person who understand the needs of
stakeholders and communicate them to developer. There
attributes play a significant role in requirements elicitation.
The attribute considered for the framework are
Analyst’s Industrial Knowledge (Low, Medium, High),
Analyst Experience (Fresher, Experienced), Problem
domain knowledge (Low, Medium, High). The Graph 5
depicts the relationship between analyst Characteristics and
requirements elicitation techniques.
Graph 3. Elicitation Techniques Vs Analyst
Characteristics
IV. CASE STUDIES FOR EXAMINING THE
WORKING OF FRAMEWORK
The section below discusses about the suitability of
proposed framework using three case studies. We have
applied the approach to Online Examination System, Port
Scheduling System and E-Governance Lok Mitra project.
Each of the case studies has been explained below:
A.Online Examination System
It is a software resolution that facilitates any industry or
institute to arrange, conduct and manage online
examination. It permits various peoples to give the exam
and presents the results at the end of the exam. System
administrator can create, alter and remove questions from
test papers. End-uses can register themselves, login and
perform the test with his own specific id and can also see the
results as well. It is a cost-effective, less time consuming
and most popular means of mass- evaluation system.
Users of online examination system can be categories into
two kinds: Administrator and Examinee. This project has
following known characteristics.
• Project Characteristics: project size- is applicable
for educational institute (small, medium), Project
Complexity should be medium, time and cost constraints
would be medium, Project Scope can be public or private,
project safety will be high and User involvement- low.
• Process Characteristics: Waterfall Model
• Organizational Characteristics: Organizational
Size- Organization can be small/ medium as institute and
Impact of organizational culture- No
• Stakeholder Characteristics: Geographical
distribution- Same, No. of stakeholder- Group, Stakeholder
Availability Required- No, Stakeholder Experienced-
Fresher
• Analyst Characteristics: Analyst Industrial
Knowledge: High, Problem domain knowledge: high
Results: when we analyzed known attributes with
mapping table, we identified Interview, brainstorming,
repertory grid, ethnography, Introspection, JAD, Analysis
Laddering are the techniques which gives effective results.
B. Port Scheduling System
The objective of the project “Port Scheduling System” is
to schedule a container terminal with maximum of 1million
TEU (20-foot equivalent unit) throughput each year. The
terminal essentially handles small sized cargo also. The
project encompasses an extremely interactive interface and a
high degree of computerization of the control functions and
arrangement of port.
This project has following known characteristics.
• Project Characteristics: Project size: Medium,
International Journal of Engineering and Advanced Technology (IJEAT)
ISSN: 2249-8958 (Online), Volume-8 Issue-5C, May 2019
1340
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
Project complexity: Medium, Cost Constraints: High,
Project category: Semi-detached, Requirements volatility:
Low, Project Type: New, Project safety: High.
• Organizational Characteristics: Organization size:
Large, Organization and customer relationship: New
• Stakeholder Characteristics: No. of stakeholder-
Single.
• Analyst Characteristics: Analyst Industrial
Knowledge: High, Problem domain knowledge: High
Results: when we analyzed known attributes with
mapping table, we identified Interview, Ethnography, JAD,
Card sorting are best techniques which produces effective
results.
C. Lok Mitra
It is the first electronic service in the state of Rajasthan.
Its purpose is to arrange Information Technology for the
assistance of the common people. With this, people get well-
organized effective services through IT driven interfaces. It
is an e-governance project in which a single server is
connected to different Departmental servers via Devoted
Leased Line & Dial-up Network with various electronic-
counters, which can manage all related services. It also
provided facilities of making payments with the help of
Internet by means of Credit Card.
Lok Mitra majorly having types of users- Administrator
and Citizens. Following listed some known characteristics:
• Project Characteristics: Project size- Large, project
Complexity should be high, time and cost constraints would
be medium, Project Scope can be public, Project Status-
existing, project safety will be high and User involvement-
high.
• Process characteristics: Waterfall Model
• Organizational Characteristics: Organizational
Size- Organization can be large and Impact of
organizational culture- existing.
• Stakeholder Characteristics: Geographical
distribution- Same, No. of Stakeholder- Group, Stakeholder
Availability Required- Yes, Stakeholder Experienced-
Fresher
• Analyst Characteristics: Analyst Industrial
Knowledge: High, Problem domain knowledge: Medium
Results: when we analyzed known attributes with
mapping table, we identified card sorting, survey, Interview,
Brainstorming, introspection and analysis laddering are the
techniques which gives effective results.
V. CONCLUSION
In this paper, we have presented a meaningful deep
insight into various types of requirements elicitation
techniques along with their strengths and weaknesses.
Requirements Elicitation process is extremely affected by
stakeholder characteristics, software project attributes,
software process model involved and organizational
attributes. Elicitation technique has possessed specific set of
unique features that is focused to related application. In this
paper, we outline a way to elect a set of requirements
elicitation methods for getting the best results in
requirement elicitation process. A mapping table is created
for each factor with respect to requirements elicitation
techniques. Problem domain is a known attribute for the
problem under construction. It acts as an input for mapping
table and results will be the set of effective elicitation
techniques that gives optimal results for gathering
requirements. The requirements elicitation is still one of the
major challenging area in software development. By
examining problem domain with respect to above mentioned
five factors helps the effective way to make an optimal
choice of picking requirements elicitation techniques. Future
work is to identify other factors and incorporate it in this
framework for making it better way to select best
requirement elicitation techniques for particular
circumstances.
REFERENCES
1. Bourque, P. and Fairley, R.E. “Guide to the software
engineering body of knowledge”, Version 3.0. IEEE
Computer Society. Retrieved April 2, 2019, from
www.swebok.org,.https://www.computer.org/education/bodi
es-of-knowledge/software-engineering
2. Mulla, N. and Girase, S. “A new approach to requirement
elicitation based on stakeholder recommendation and
collaborative filtering”. International Journal of Software
Engineering & Applications (IJSEA), 3(3), 51-61, 2012.
3. Sommerville, I. Software engineering (9th ed.). Boston:
AddisonWesley,(2011)..https://inspirit.net.in/books/academic
/Ian%20Sommerville%20Software%20Engineering,%209th
%20Edition%20%20%20%202011.pdf
4. Batra, Mona and Bhatnagar Dr. Archana, “Requirements
Prioritization: A Review”, International Journal of Advanced
Research in Science, Engineering and Technology, Vol. 3,
Issue 11, November 2016.
http://www.ijarset.com/upload/2016/november/6_IJARSET_
monabatra.pdf
5. Pressman, R. Software engineering: a practitioner's approach
(7th ed.). New York: McGraw-Hill higher
education,2010.http://dinus.ac.id/repository/docs/ajar/RPL7t
h_ed_software_engineering_a_practitioners_approach_by_ro
ger_s._pressman_.pdf
6. Nuseibeh, B.; and Easterbrook, S. Requirements engineering:
a roadmap. Proceedings of the 22nd International Conference
on Software Engineering ICSE'00. Limerick, Ireland, 4-11,
2000.
https://www.cs.toronto.edu/~sme/papers/2000/ICSE2000.pdf
7. Pohl, K. Requirements engineering: Fundamentals,
principles, and techniques. Springer. Berlin, Germany, 2010.
http://elearn.dsum.org/pluginfile.php/2357/mod_resource/con
tent/0/_Klaus_Pohl_Chris_Rupp_Requirements_Engineering
_b-%20%281%29.pdf
8. Wiegers, K. E. (1999). Software requirements. Microsoft
Press.https://dl.acm.org/citation.cfm?id=519610
9. Batra, Mona and Bhatnagar Dr. Archana “A Comparative
Study of Requirements Engineering Process Model”
International Journal of Advanced Research in Computer
Science, Volume 8, No. 3, March – April
2017.https://www.academia.edu/35642649/A_Comparative_
Study_of_Requirements_Engineering_Process_Model
10. Batra, Mona and Pandey S.K., “Security Testing in
Requirements Phase of SDLC”, International Journal of
Computer Applications (0975 – 8887) Volume 68– No.9,
April 2013.
11. Batra, Mona and Bhatnagar Dr. Archana, “Descriptive
Literature Review of Requirements Engineering Models”,
International Journal of Advanced Research in Computer
Science and Software Engineering, Volume 5,
Issue2,February2015.http://ijarcsse.com/Before_August_201
7/docs/papers/Volume_5/2_February2015/V5I2-0331.pdf
International Conference on Recents Advancements in Engineering and Technology (ICRAET-18) |15th and 16th
March 2019|Siddhartha Institute of Technology & Sciences, Telangana, India.
1341
Published By:
Blue Eyes Intelligence Engineering
and Sciences Publication (BEIESP)
© Copyright: All rights reserved.
Retrieval Number: E11900585C19/2019©BEIESP
DOI:10.35940/ijeat.E1190.0585C19
Journal Website: www.ijeat.org
12. Bell T.E. and Thayer T.A., “Software requirements: are they
really a problem”, 2nd International Conference on Software
engineering, pp 61-68, IEEE Computer Society
Press,1976.https://pdfs.semanticscholar.org/a50d/8f564d063e
526e94114875220440f64d8666.pdf
13. Loucopoulos, P. and Karakostas, V. System requirements
Engineering. New York: McGraw-Hill, 1995.
https://dl.acm.org/citation.cfm?id=545779
14. Borland Software Corporation, “Mitigating risk with
effective requirements engineering how to improve decision-
making and opportunity through effective requirements
engineering”. Part two in a series about understanding and
managing risk.
15. Bohem, B.R.W. (1981). Software engineering economics.
New Jersey: Prentice - Hall.
16. Coulin, C., Zowghi, D., “Requirements Elicitation for
Complex Systems: Theory and Practice, in Requirements
Engineering for Socio-Technical Systems”, 20.0
17. Zhang Zheying, “Effective Requirements Development - A
Comparison of Requirements Elicitation techniques”,
SQM2007–International Conference on Strangeness in Quark
Matter.
http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.13
5.185&rep=rep1&type=pdf
18. Lloyd W. J., Rosson M. B. and Arthur J. D., “Effectiveness
of elicitation techniques in distributed requirements
engineering", Proceedings of the IEEE International
Conference on Requirements Engineering, 2002, pp. 311–
318. https://doi.org/10.1109/ICRE.2002.1048544
19. Gunda S. G., “Requirements engineering: elicitation
techniques,” M.S. thesis, Department of Technology,
Mathematics and Computer Science, University West,
Sweden, 2008. http://www.diva-
portal.org/smash/get/diva2:215169/fulltext01
20. Joseph Elijah , “Survey on Requirement Elicitation
Techniques: It's Effect on Software Engineering”,
International Journal of Innovative Research in Computer
and Communication Engineering, Vol. 5, Issue 5, May
2017.http://www.ijircce.com/upload/2017/may/1_SURVEY.
pdf
21. Tiruneh1 Theodros and Mishra Manish Kumar, “Analysis
and Performance Evaluation of Requirement Elicitation
Techniques”, International Journal of Computer Sciences and
Engineering, VOLUME 6, Issue 4, April
2018.https://www.ijcseonline.org/pdf_paper_view.php?paper
_id=1855&18-IJCSE-03167.pdf
22. Sharma Shreta and Pandey S. K., “Revisiting Requirements
Elicitation Techniques”, International Journal of Computer
Applications (0975 – 8887) Volume 75– No.12, August
2013.https://pdfs.semanticscholar.org/692b/30d03ab7f1fd797
327d26d2392008b8e3a93.pdf
23. Khaled Almakadmeh and Hanan Al-Zawahreh, “Procedural
Model of Requirements Elicitation Techniques”,
International Conference on Intelligent Information
Processing, Security and Advanced Communication, At
Batna, Algeria, November
2015.https://www.researchgate.net/publication/280154366_P
rocedural_Model_of_Requirements_Elicitation_Techniques
24. Sajjad Umar and Hanif Muhammad Qaisar, “Issues and
Challenges of Requirement Elicitation in Large Web
Projects”, Master Thesis, School of Computing, Blekinge
Institute of Technology, Sweden, January
2010.https://www.diva-
portal.org/smash/get/diva2:830517/FULLTEXT01.pdf
25. Zhang Z., “Effective Requirements Development – A
Comparison of Requirements Elicitation techniques”,
Tampere, Finland, Published in
SQM2007.http://citeseerx.ist.psu.edu/viewdoc/download?doi
=10.1.1.135.185&rep=rep1&type=pdf
26. Batra Mona and Bhatnagar Dr. Archana Bhatnagar, “An
Experimental Survey to Find Application Specific Elicitation
Technique”, 4th International Conference on “Computing for
Sustainable Global Development”, 01st - 03rd March, 2017
Proceedings of the 11th INDIACom, 2017 New Delhi
(INDIA).
27. Arif Mohd. and Sarwar Saoud, “Identification of
Requirements using Goal Oriented Requirements Elicitation
Process”, International Journal of Computer Applications
,Volume 120 – No.15, June
2015.https://research.ijcaonline.org/volume120/number15/px
c3904070.pdf
28. Sadiq M, A Jawed, Asim M, Qureshi A, Suman R, “More on
Elicitation of Software requirements and prioritization using
AHP”, IEEE International Conference on Data Storage and
Data Engineering pp 232-236, February 2010, Bangalore,
India.
29. Kelly G The psychology of personal constructs, Norton, New
York,
(1955).https://www.researchgate.net/profile/Gabriele_Chiari
2/publication/317064022_George_A_Kelly_and_His_Person
al_Construct_Theory_iBook/links/5923eceda6fdcc4443fa3cf
4/George-A-Kelly-and-His-Personal-Construct-Theory-
iBook.pdf
30. Tiwari Saurabh, Rathore Singh Santosh, and Gupta Atul,
“Selecting Requirement Elicitation Techniques for Software
Projects”, CSI 6th International Conference on Software
Engineering, CONSEG 2012
31. Paetsch, F., Eberlein, A. and Maurer, F., “Requirements
Engineering and Agile Software Development. Enabling
Technologies”. pp. 308-313, IEEE, 2003.
32. Anwar Fares and Razali Rozilawati, “A Systematic
Stakeholders and Techniques Selection Framework for
Software Requirements Elicitations, Journal of Theoretical
and Applied Information Technology, Vol.96. No 16, Last
Retrieved on 9 June 2019.
http://www.jatit.org/volumes/Vol96No16/21Vol96No16.pdf
